The maintainer of the Axios npm package confirmed that the supply chain reduction was the result of a highly targeted social engineering campaign orchestrated by North Korean threat actors tracked as UNC1069.
Guardian Jason Saayman he said that the attackers agreed to their social engineering efforts “especially for me” by starting to approach him under the guise of the founder of a recognized, well-known company.
“They shaped the company’s founders as well as the company itself,” Saayman said in a postmortem of the event. “Then they invited me to the virtual Slack space. This workspace was named the company’s CI and it was named logically. The Slack [workspace] it was very well thought out; they had channels where they shared LinkedIn posts.”
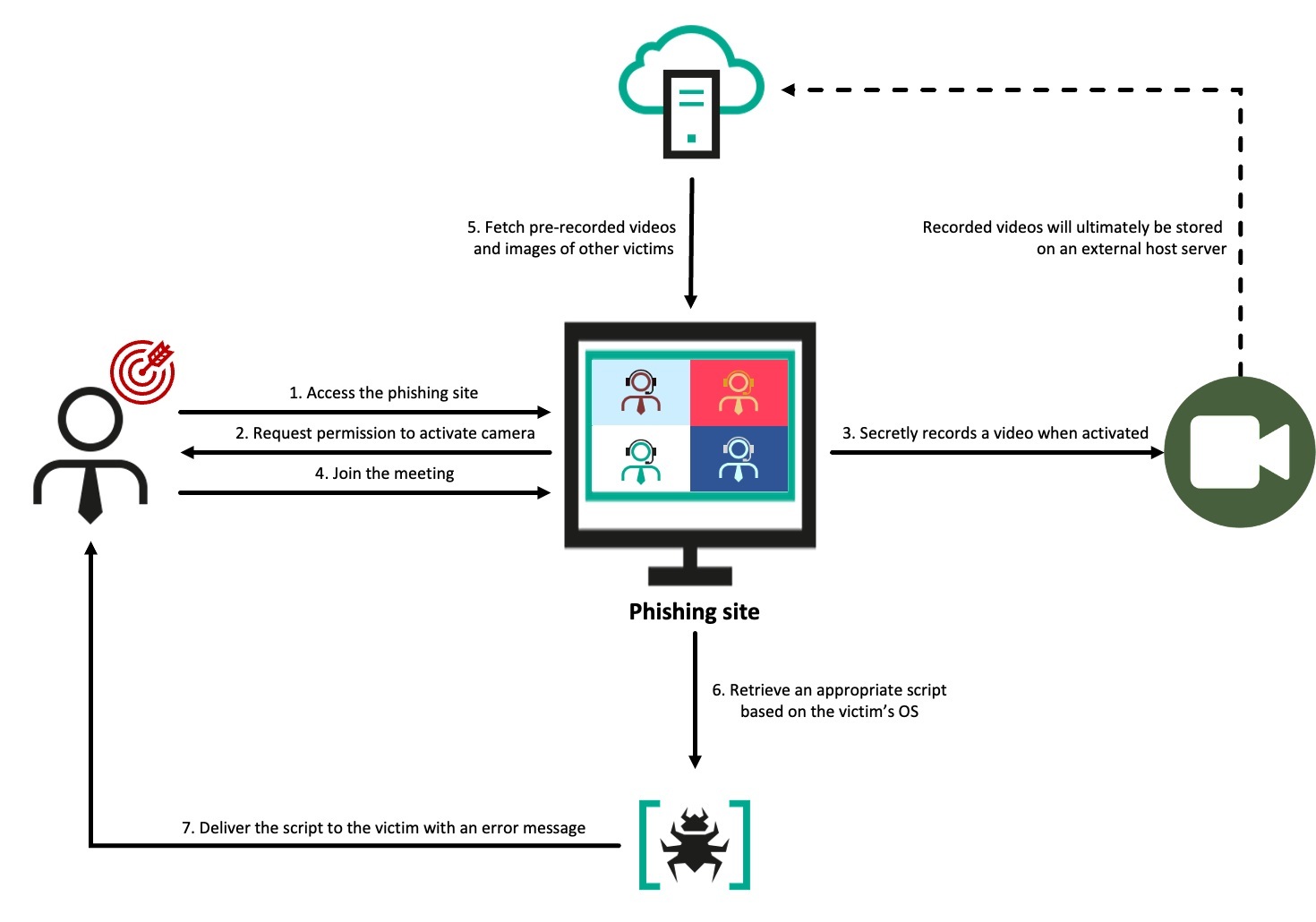
After that, the threat actors allegedly arranged a meeting with him on Microsoft Teams. When he joined the fake phone, he was presented with an error message that said “something on my system is out of date.” Once the update started, the attack led to the delivery of a remote trojan.
The access provided by the trojan enabled attackers to steal the npm account information needed to publish two trojanized versions of the Axios npm package (1.14.1 and 0.30.4) containing an implant called WAVESHAPER.V2.
“Everything was well coordinated, looked right, and was done professionally,” Saayman added.
 |
| Source: Kaspersky |
The series of attacks described by the project manager shares many similarities with the business associated with UNC1069 and BlueNoroff. The details of this campaign were largely documented by Huntress and Kaspersky last year, and the latter followed it up under the moniker GhostCall.
In these attacks, users are shown an error message seconds after logging in, stating that their system is not working properly and instructing them to download the malicious Zoom or Teams SDK via a ClickFix pop-up message. Depending on the victim’s operating system, this action leads to the execution of an AppleScript (for macOS) or a PowerShell script (for Windows).
One of the malicious payloads installed as part of the attack chain is a macOS backend based on Nim (or the version of Go written for Windows) called CosmicDoor that provides a complete hacking tool called SilentSiphon to take information from browsers and password managers, and secrets related to GitHub, GitLab, PitLab, Python RubyGems, Rust argo, and .NET NuGet.
“Historically, […] these special guys have gone after crypto founders, VCs, public figures,” security researcher Taylor Monahan said. “They’re public engineers and they take over their accounts and target the following people. This change in targeting [OSS maintainers] it is a matter related to my opinion. “

As preventive measures, Saayman described several changes, including restoring all tools and data, creating immutable releases, accepting the OIDC flow for publishing, and improving GitHub Actions to use best practices.
Studies show how open source project maintainers are increasingly becoming the target of sophisticated attacks, allowing threat actors to target low-level users in large numbers by publishing toxic versions of popular packages.
Since Axios attracts around 100 million downloads every week and is widely used in the JavaScript environment, the explosive scope of such a feed-forward attack could be huge as it spreads rapidly with direct and overarching dependencies.
“A widely used package like Axios being compromised shows how difficult it is to rationalize vulnerabilities in the modern JavaScript environment,” Socket’s Ahmad Nassri said. “It’s a property of how the decision to depend on the environment works today.”
#UNC1069 #Social #Engineering #Axios #Maintainer #Led #npm #Supply #Chain #Attack
