Cybersecurity researchers have discovered a Russian remote access tool that distributes malicious Windows (LNK) files disguised as private folders.
The CTRL The toolkit, according to Censys, is custom-built using .NET and includes various functions” to facilitate phishing, keylogging, Remote Desktop Protocol (RDP) hijacking, and tunneling with Fast Reverse Proxy (FRP).
“The apps offer encrypted streaming, credential harvesting with a custom Windows Hello phishing UI, keylogging, RDP session hijacking, and proxy recovery with FRP,” Censys security researcher Andrew Northern said.
The attack site control platform said it found CTRL in an open directory at 146.19.213.[.]155 on February 2026. Attack chains that distribute the toolkit rely on a weaponized LNK file (“Private Key #kfxm7p9q_yek.lnk”) with a folder icon to trick users into double-clicking it.
This leads to many steps, and each step destroys or reduces the next one, until it leads to the deployment of the equipment. The LNK file droplet is designed to launch a hidden PowerShell command, then deletes existing persistent processes from the victim’s Windows Startup window.

It also decodes the encoded Base64 blob and moves it to memory. Stager, for its part, attempts a TCP connection to hui228[.]ru: 7000 and download the next level charges from the server. In addition, it modifies firewall rules, creates persistence using scheduled tasks, creates local background users, and launches a cmd.exe shell server on port 5267 accessible through an FRP tunnel.
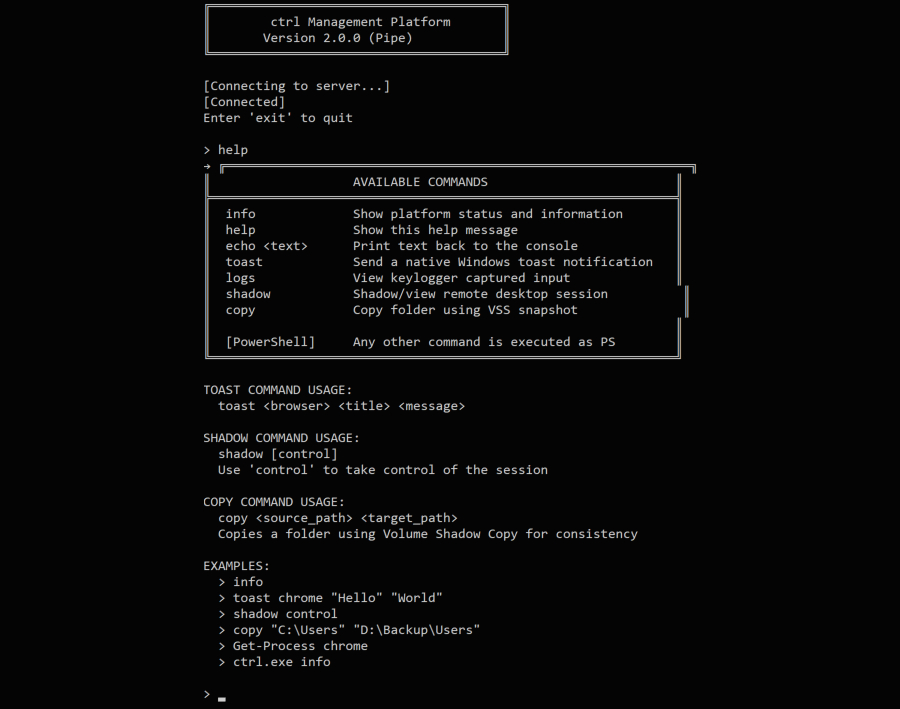
One of the downloads, “ctrl.exe,” acts as a .NET loader for launching the embedded flow, CTRL Management Platform, which can act as a server or client based on command line arguments. Communication takes place through a pipe called Windows.
“The two-way model means that the operator executes ctrl.exe once on the victim (via the platform), then interacts with it by running the ctrl.exe client through an FRP-encrypted RDP session,” Censys said. “A structure called a pipeline keeps all the C2 command traffic at the victim machine – nothing goes through the network except the RDP session itself.”
Supported commands allow the malware to collect system information, launch a module designed for data harvesting, and start a keylogger as a background service (if configured as a server) to capture all keystrokes in a file named “C:\Temp\keylog.txt” by installing a keyboard hook, and display the results.
The harvesting script component is implemented as a Windows Presentation Foundation (WPF) application that simulates a real Windows PIN authentication message to capture a system PIN. The module, in addition to preventing attempts to escape the phishing window with keyboard shortcuts such as Alt+Tab, Alt+F4, or F4, verifies the entered PIN against the real Windows process using UI automation using the SendKeys() method.
“If the PIN is rejected, the victim is redirected with an error message,” Northern explained. “The window remains open even if the PIN is successfully verified against the Windows authentication system. The captured PIN is prefixed. [STEALUSER PIN CAPTURED] to the same keylog file used by the background keylogger.”
One of the built-in commands in the toolkit allows sending automatic toast notifications to web browsers such as Google Chrome, Microsoft Edge, Brave, Opera, Opera GX, Vivaldi, Yandex, and Iron to perform additional identity theft or provide other payloads. Two more payloads dropped as part of the attack are listed below –
- FRPWrapper.exe, which is a Go DLL installed in memory to create RDP tunnels and a raw TCP shell with the operator’s FRP server.
- RDPWrapper.exe, which enables unlimited RDP sessions.
“The toolkit shows operational security on purpose. None of the three received binaries contain hard-coded C2 addresses,” Censys said. “All data encryption takes place through the FRP tunnel via RDP – the operator connects to the victim’s computer and reads the keylog information with a pipe called ctrl. This architecture leaves less network forensic tools compared to the usual C2 beacon methods.”
“CTRL toolkit shows a trend towards purpose-built, single-function toolkits that prioritize operational security over feature-width. By routing all interactions through FRP reverse tunnels to RDP sessions, the operator avoids the beacon patterns seen by the network that identify proprietary RATs.”
#Russian #CTRL #Toolkit #Malicious #LNK #Files #Hijacks #RDP #FRP #Tunnels
