Threat actors are using HTTP cookies as a control channel for PHP-based web shells on Linux servers and to achieve remote code execution, according to findings from the Microsoft Defender Security Research Team.
“Instead of exposing command processing through URL parameters or application entities, these web shells rely on the value of cookies provided by actors for gateway processing, command forwarding and malicious execution,” said the tech giant.
This method provides additional stealth as it allows the malicious code to remain silent during normal operation and to activate the web shell logic only when there is a certain cookie value. This behavior, Microsoft noted, extends to web applications, scheduled jobs, and trusted back-office workers.
The malware takes advantage of the fact that the cookie value is available at runtime via the $_COOKIE superglobal variable, which allows the attackers’ entries to be used without further inspection. Additionally, this method is less likely to raise red flags when cookies interact with normal web traffic and reduce visibility.
The cookie-managed operating system comes in different implementations –
- A PHP loader that uses multiple layers of obfuscation and runtime checks before splitting the cookies configured to execute the second loaded load.
- A PHP script that parses the cookie data is configured to rebuild functions such as file handling and editing functions, and optionally writes the second payload to disk and executes it.
- A PHP script that uses a single cookie value as a pointer to trigger actor-controlled actions, including rendering and uploading files.
In at least one instance, threat actors have been found to gain initial access to a Linux environment hosted by a victim with proper credentials or the use of known security vulnerabilities to create a cron job that invokes a shell routine to periodically load the PHP loader.
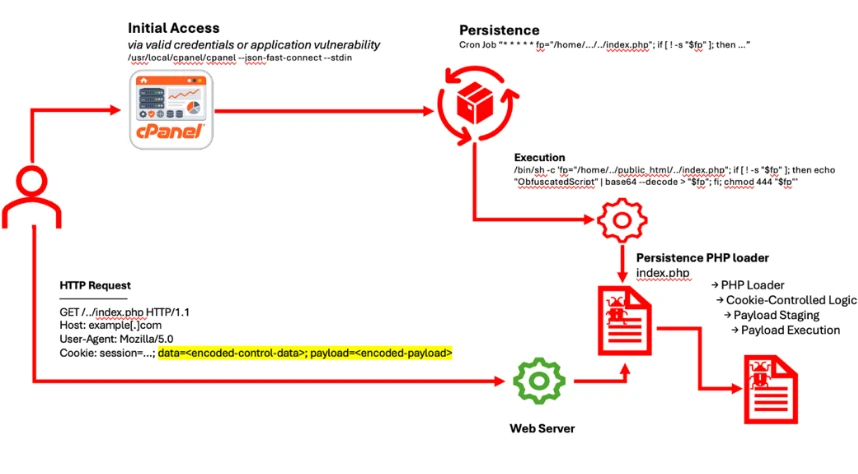
This “self-healing” feature allows the PHP loader to be restarted frequently by a scheduled task even if it was removed as part of a cleanup and maintenance effort, thus creating a reliable and stable code execution channel. Once the PHP loader is installed, it stays idle during normal traffic and starts running when it receives HTTP requests with special cookie values.
“By switching performance management to cookies, the web shell can remain hidden from normal traffic, only active during intentional interactions,” Microsoft added. “By separating persistence and re-establishment from process control through cookie-gated processing, the threat actor reduced the operational noise and the weak signals seen in conventional operating systems.”
The common thing that combines the above-mentioned process is the use of obfuscation to hide the sensitive process and cookies based on cookies to start the malicious action, while leaving less room for intervention.

To prevent the threat, Microsoft recommends enforcing multi-factor authentication for control panels, SSH access, and administrative connections; monitoring for abnormal log-in activity; preventing the creation of shell translators; checking cron jobs and scheduled jobs on web servers; monitoring the presentation of suspicious files in web directories; and reduce the capacity of control panel shells.
“The persistent use of cookies as a control mechanism suggests the re-use of commercial web shells,” Microsoft said. “By changing the control logic to cookies, threat actors enable persistent post-compromise access that can bypass more traditional inspection and logging controls.”
“Instead of relying on complex exploit chains, the threat actor used legitimate execution methods already in the environment, including web server applications, control panel components, and cron tools, to create and maintain malicious code.”
#Microsoft #Details #CookieManage #PHP #Web #Shells #Persistent #Cron #Linux #Servers
