The new campaign deployed the ClickFix social engineering tactic as a way to distribute an unregistered malware tool called. DeepLoad.
“It probably uses AI-assisted confusion and process injection to avoid persistent scanning, while identity theft starts immediately and captures passwords and programs even if the main machine is turned off,” ReliaQuest researchers, Thassanai McCabe and Andrew Currie said in a report shared with The Hacker News.
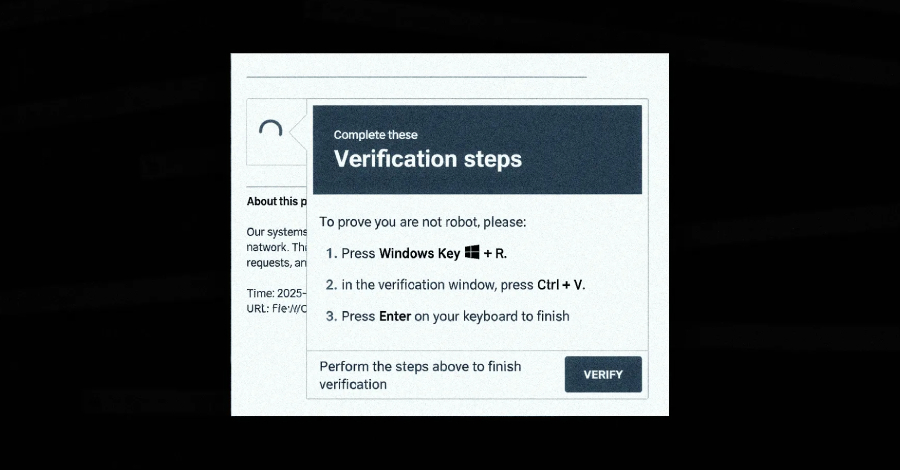
The starting point of the attack chain is a ClickFix trap that tricks users into running PowerShell commands by entering a command in the Windows Run dialog under the guise of solving a problem that doesn’t exist. This, in turn, uses “mshta.exe,” a legitimate Windows tool to download and run an invisible PowerShell tool.
The loader, for its part, has been found to hide its real operation among various trivial tasks, perhaps in an attempt to fool security devices. It is assessed that threat actors rely on artificial intelligence (AI) tools to develop an obfuscation layer.

DeepLoad makes a deliberate effort to adapt to the standard Windows operating system and fly under the radar. This involves hiding the payload inside “LockAppHost.exe,” a legitimate Windows process that manages the lock key.
In addition, the malware covers its tracks by turning off PowerShell command history and targeting Windows core functions directly instead of relying on built-in PowerShell commands to launch applications and modify memory. In doing so, it bypasses the usual monitoring hooks that keep tabs on PowerShell-based operations.
“To avoid file discovery, DeepLoad generates a second component on the fly using PowerShell embedded in Add-Type, which compiles and runs code written in C#,” ReliaQuest said. “This generates a temporary Dynamic Link Library (DLL) file that is placed in the user’s Temp directory.”
This provides a way for malware to bypass file name detection, as the DLL is compiled every time it is created and written with a random file name.
Another notable security evasion technique adopted by DeepLoad is the use of asynchronous process call (APC) injection to run a large load within a trusted Windows process without a formal payload written to disk after starting the target process in a suspended state, writing shellcode to its memory, and then starting the process.
DeepLoad is designed to facilitate identity theft by extracting browser passwords from the host. It also drops a malicious browser extension that blocks data as it is entered on login pages and persists across user sessions unless explicitly removed.
Even more dangerous is the malware’s ability to disguise itself when removable media devices such as USB drives are connected and copy files containing malware with names like “ChromeSetup.lnk,” “Firefox Installer.lnk,” and “AnyDesk.lnk” so that it can trigger an infection once it is double-clicked.
“DeepLoad used Windows Management Instrumentation (WMI) to capture a ‘clean’ host three days later with no user activity and no attacker interaction,” ReliaQuest explained. “WMI served two purposes: It broke the parent-child process chains most of the detection rules were built to handle, and it created a WMI event registry that silently re-ran the attack later.”
The goal, it seems, is to use a lot of malware that can perform malicious actions throughout the chain of cyber killing and detect it remotely by security systems by avoiding writing old things to disk, mixing Windows processes, and quickly spreading to other machines.
The announcement comes as G DATA has detailed another malware tool called Kiss Loader that is distributed via Windows Internet Shortcut files (URL) attached to phishing emails, then connects to a remote WebDAV application hosted on the TryCloudflare site to deliver a second shortcut that disguises itself as a PDF document.
Once executed, the shortcut generates a WSH script responsible for running the JavaScript component, which continues to retrieve and create a batch script that displays the decoy PDF, places persistence in the startup folder, and then downloads the Python-based Kiss Loader. In the latter case, the payload decrypts and runs Venom RAT, a variant of AsyncRAT, using APC injection.
It is currently unknown how widespread the attacks that run Kiss Loader are, and whether they are offered under a malware-as-a-service (MaaS) model. That said, the threat actor behind the machine claims to be from Malawi.
#DeepLoad #Malware #ClickFix #WMI #Persistence #Steal #Browser #Information