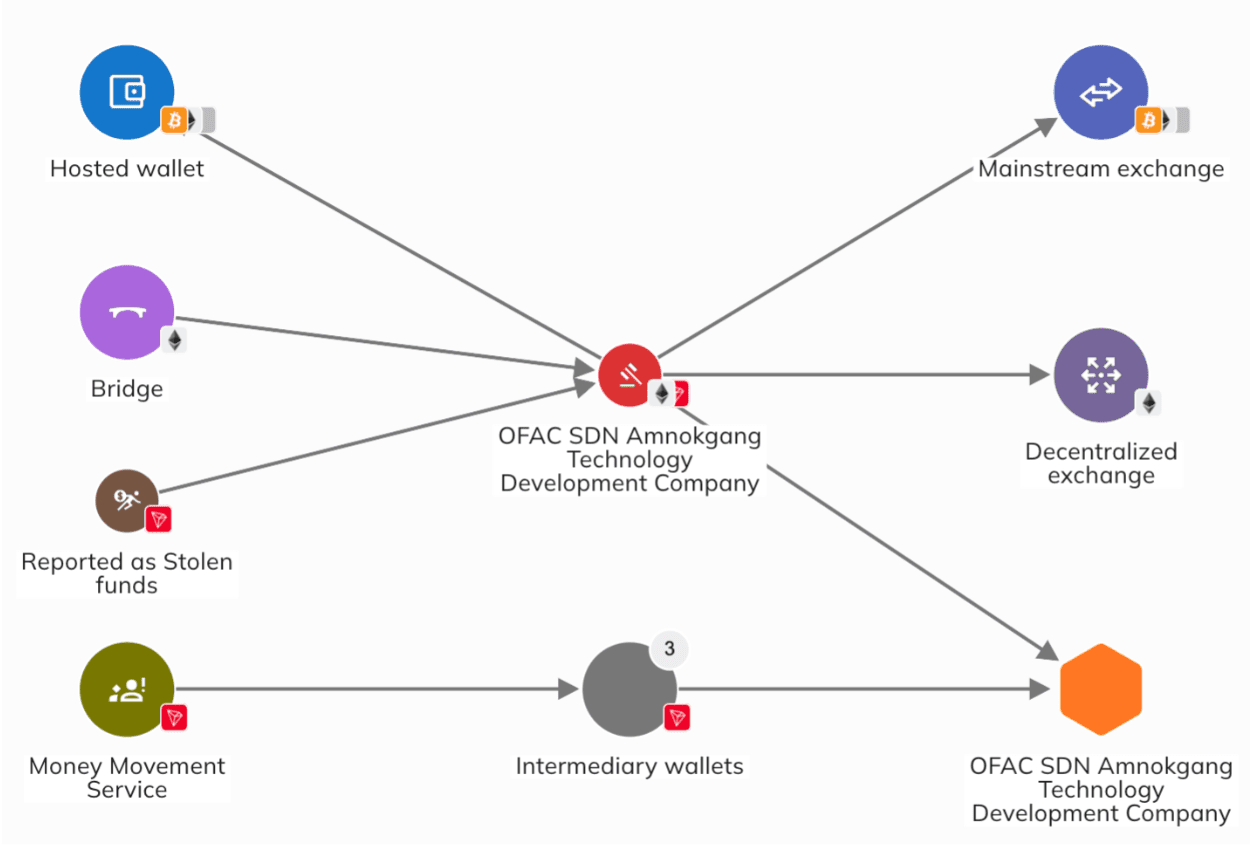
Drift revealed that the April 1, 2026 attack, which led to the theft of $285 million was the culmination of a months-long civil engineering operation by the Democratic People’s Republic of Korea (DPRK) that began in the fall of 2025.
The Solana-based exchange described it as “an attack six months in the making,” he said with moderate confidence in the North Korean government-backed hacking group. UNC4736which is also traced under the cyptonyms AppleJeus, Citrine Sleet, Golden Chollima, and Gleaming Pisces.
The threat actor has a history of targeting the cryptocurrency sector for financial theft since at least 2018. It is best known for the X_TRADER/3CX supply chain breach in 2023 and the $53 million takedown of decentralized finance (DeFi) platform Radiant Capital in October 2024.
“The basis of this connection is both the chain (the funds used to stage and monitor this operation back to the Radiant attackers) and the operation (the people sent throughout this campaign have a known operation related to the DPRK),” Drift said in an analysis on Sunday.
In an analysis published at the end of January 2026, the cybersecurity company CrowdStrike described Golden Chollima as an offshoot of Labyrinth Chollima aimed at cryptocurrency theft by targeting small fintech firms in the US, Canada, South Korea, India and Western Europe.
“The adversary typically commits low-value theft during a sustained period of activity, suggesting a responsibility to ensure basic income generation for the DPRK regime,” CrowdStrike said. “Despite improving trade relations with Russia, the DPRK needs more money to finance ambitious military projects that include building new destroyers, building nuclear-powered submarines, and developing additional reconnaissance satellites.”
In at least one incident observed in late 2024, UNC4736 delivered malicious Python packages in an attempt to recruit a European fintech company. Upon gaining access, the threat actor moved outside the victim’s cloud environment to access IAM settings and cloud-related resources, ultimately diverting cryptocurrency assets to wallets controlled by the adversary.
How A Drift Attack Can Be Found
Drift, which works with law enforcement and forensic partners to piece together the sequence of events that led to the hack, said it was the target of a “systematic intelligence operation” that required months of planning.
Starting in or around fall 2025, people pretending to be a crowdfunding company approached Drift donors at major cryptocurrency conferences and international crypto conferences under the guise of integrating the protocol. It has since emerged that this was a deliberate process, where members of this business group approached and built friendships with special Drift sponsors at various major industry meetings held in several countries over a period of six months.
“The people who appeared in person were not natives of North Korea,” explained Drift. “DPRK threat actors operating in this context are known to use third-party agents to conduct face-to-face communications.”
“They were articulate, had verifiable expertise, and were familiar with the way Drift worked. The Telegram team was formed at the first meeting, and what followed were months of intense discussions about business strategies and possible mergers.
Then, sometime between December 2025 and January 2026, the team entered the Ecosystem Vault on Drift, a step that required filling out a form with strategic information. As part of this process, individuals are said to have interacted with multiple donors, asking them “detailed and knowledgeable questions about the product,” while placing more than $1 million of their own funds.
Drift said, this was a measured step designed to build a functional presence within the Drift environment, and integration discussions are ongoing with providers until February and March 2026. This included sharing links to projects, tools and applications that the company said it was developing.
The possibility that these transactions with the trade group could have served as an initial method of infection took on significance after the April 1 operation. But as Drift revealed, their Telegram conversations with the malware were deleted as soon as the attack happened.
There are suspected to be two main attack vectors –
- One client may have crashed after merging the team’s shared code repository as part of a front-end effort for their vault.
- A second contributor was prompted to download the wallet product via Apple’s TestFlight to test the beta app.
The storage-based attack vector is believed to have installed a malicious Microsoft Visual Studio Code (VS Code) project that uses the “tasks.json” file to automatically launch the execution of malicious code on the project in the IDE by using the “runOn:folderOpen” option.
It is important to note that this method has been adopted by North Korean threat actors associated with the Contagious Interview campaign since January 2025, which led Microsoft to introduce new security controls in VS Code version 1.109 and 1.110 to prevent the unplanned operation of jobs when opening the workplace.
“Research has shown to date that the profiles used in this third-party targeting process have comprehensive information included including employment history, social-facing information and professional networks,” Drift said. “Drift contributors have met in person and seem to have spent months building profiles, both personal and professional, that can withstand scrutiny during business or peer relationships.”
Center for North Korea’s Divided Malware Ecosystem
The announcement comes as DomainTools Investigations (DTI) revealed that the DPRK’s cyber infrastructure has become “deliberately isolated” malware that is purpose-driven, active, and resistant to delivery efforts. The change is believed to be a response to law enforcement actions and intelligence disclosures about North Korea’s anti-piracy campaigns.
“Malware development and operations are increasingly separated, both technically and organizationally, to ensure that exposure in one mission area does not spread throughout the program,” the DTI said. “Importantly, this model also increases ambiguity. By separating resources, equipment, and operational methods based on mission messages, the DPRK complicates production and delays defender decision-making.”
To that end, DomainTools noted that the DPRK’s espionage-focused malware track is closely related to Kimsuky, while the Lazarus group leads efforts to generate illegal income for the government, becoming a “central pillar” for evading sanctions. The third track is about running ransomware and wiper malware for the purpose of strategic display and drawing attention to its capabilities. This destructive branch is associated with Andariel.
Social Engineering Behind Contagious Communication and IT Employee Fraud
Social engineering and deception continue to be the main cause of interference by many of the so-called DPRK threat actors. This includes the recent release of the most popular npm package, Axios, as well as ongoing campaigns such as Contagious Interview and IT employee theft.
Infectious communication is the moniker assigned to a long-running threat in which an adversary approaches potential victims and tricks them into executing malicious code from a fake repository as part of a test. Some of these tests used weaponized Node.js projects hosted on GitHub to install a JavaScript backend called DEV#POPPER RAT and an information thief known as OmniStealer.
On the other hand, the theft of DPRK IT workers refers to the coordinated efforts of North Korean workers to find volunteer and full-time jobs in Western companies using stolen information, AI-generated people, and fake credentials. Once hired, they generate income and use the opportunity to introduce malware and siphon sensitive information and content. In some cases, stolen data is used to defraud businesses.

The government-sponsored program employs thousands of skilled workers in countries like China and Russia, who plug into company-issued laptops held at laptop farms in the US and elsewhere. The scheme also relies on a network of assistants to receive work laptops, manage salaries, and handle supplies. These helpers are recruited through shell companies.
The process begins with employers identifying and identifying potential candidates. Once accepted, IT workers enter the onboarding phase, where mentors assign identities and profiles, and guide them through resume updates, interview preparation and initial job applications. Threat actors also work with colleagues to fulfill hiring requirements for full-time opportunities where strict identity verification policies are enforced.
As noted by Chainalysis, cryptocurrency plays an important role in sending most of the income generated by these IT worker projects back to North Korea while avoiding international sanctions.
“The cycle is endless. North Korean IT workers understand that, sooner or later, they will quit or be fired from any job,” Flare and IBM X-Force said in a report last month. “As a result, they constantly switch between jobs, identities and accounts – never staying in the same place or using the same person for long.”
New evidence uncovered by Flare has revealed the campaign’s efforts to recruit people from Iran, Syria, Lebanon and Saudi Arabia, with at least two Iranians receiving letters from US employers. There have been more than 10 cases of Iranian citizens being recruited by the government.
Managers have also been found to be using LinkedIn to recruit expats from Iran, Ireland and India, who are then trained to find jobs. These people, called callers or interviewers, get on the phone with American hiring managers, go through technical interviews, and impersonate real or fake Westerners they have observed. When a caller fails to communicate, the facilitator reviews the recording and provides feedback.
“The North Koreans are deliberately targeting US defense contractors, cryptocurrency exchanges and financial institutions,” Flare said. “Although the main motivations appear to be financial, the deliberate intent shown in their documents indicates that there may be other motives as well.”
“The DPRK is not only using its own citizens under false identities. It is building a multinational recruitment pipeline, which draws artists from Iran, Syria, Lebanon and Saudi Arabia to an infrastructure intended to enter US defense contracts, stock exchanges, financial institutions, and businesses of all sizes.
#Million #Drift #Hack #Traces #DPRKs #SixMonth #Civil #Engineering #Operation
